Introduction
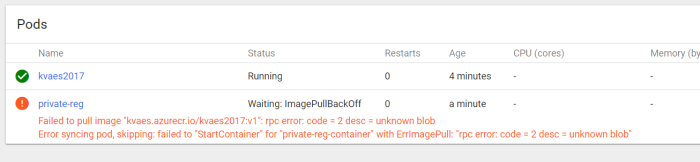
When you are deploying an image, which is hosted on a private registry, to a kubernetes (k8s) cluster with windows nodes… Then you might get the following error ;
Failed to pull image “kvaes.azurecr.io/kvaes2017:v1“: rpc error: code = 2 desc = unknown blobError syncing pod, skipping: failed to “StartContainer” for “private-reg-container” with ErrImagePull: “rpc error: code = 2 desc = unknown blob”
Context
So what did my setup look like?
- Orchestrator : Kubernetes for Windows (Azure Container Service)
- Registry : Private (Azure Container Registry)
- Image : Windows Nano Based
Technical Check
The first I’ll deploy via yaml, which is basically the example from the kubernetes docs on pulling an image from a private repo…
Now the second one is an adaptation of the example flow from the Azure Container Service documentation ;
Now let’s see how that one went…
The first one failed, and the second one passed! What was the difference?
"nodeSelector": {
"beta.kubernetes.io/os": "windows"
}
Apparently this one forces the switch to “windows container mode” (or something like that…). As it seems very similar to the following thread…
TL;DR
When deploying windows containers to a kubernetes cluster. be sure to the set the “nodeSelector” or you might end up with errors on pulling the image.